Cyber
Blog_
Decoding the latest AI-powered scams, UPI fraud tactics, and cyber threats targeting India. Written for real people, not just security professionals.
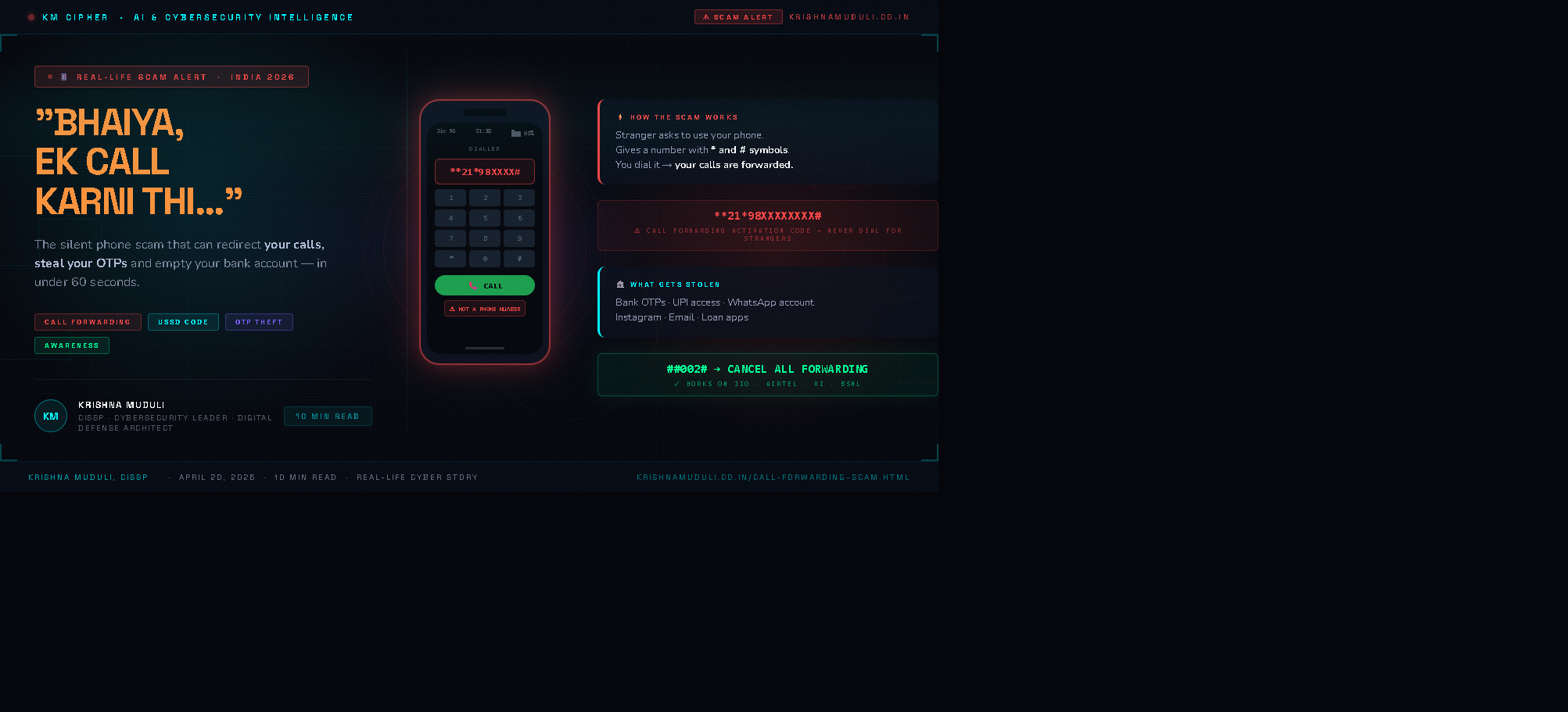
"Bhaiya, Bas Ek Call Karni Thi…" — The Phone Scam That Steals Your OTPs 😨
A stranger at the railway station asked to borrow a phone — and gave a number with stars and hash symbols to dial. It was nearly a call forwarding scam. Here's what you need to know.

GPT-5.4 in Cybersecurity: Capabilities, Use Cases & How It Compares to Claude Mythos 🤖🔐
A CISSP's deep-dive into GPT-5.4's real cybersecurity capabilities, enterprise use cases, the dual-use risk, and an expert head-to-head against Anthropic's Claude Mythos Preview.

Project Glasswing & Claude Mythos Preview 🦋🔐
Anthropic just launched Project Glasswing — a $100M AI cybersecurity initiative using a secret model called Claude Mythos Preview. Here's what it means for you.

How AI is Changing Cybersecurity Jobs in India 2026 🚀
Which roles survive, which roles grow, and how to future-proof your cybersecurity career in the AI era — with India salary data.

10 Ways to Secure Your UPI in 2026 📱💰
From AI voice cloning calls to fake payment links — discover the "Golden Rules" to completely secure your bank account.

“Papa, main bol raha hoon…” — AI voice scam se ₹5 lakh ka fraud 😨
The AI Voice Scam that shook a Bangalore family. Ramesh ji, an accidental ₹5 Lakh transfer, and the terrifying truth about modern voice cloning.

The Rise of AI Voice Scams: Why Your Voice is the New Password
With just 30 seconds of your voice from a social media post, AI can now clone your speech with 99% accuracy. Here is how scammers are targeting families.

Scanning QR Codes in Public? Here's the Silent Threat
Learn how "Qshing" works and how malicious QR codes are taking over restaurant tables and parking meters across India.

Protecting Senior Citizens from Cyber Extortion
A practical guide for families to secure their elderly parents' digital footprint and prevent social engineering attacks.

Remote Work: The Secret Vulnerabilities in Your Home Router
Why your default ISP router is the weakest link in your office security and how to harden it in under 10 minutes.

Deepfake Video Calls: Can You Trust a Video Call in 2026?
Real-time deepfake technology is being weaponized in business scams. Learn the telltale signs and how to verify identity.

Is Your Child Safe Online? A Parent's Cybersecurity Checklist
From gaming scams to predatory social media, a practical guide to protecting children in the digital age.
Subscribe to Intel Feed
Get exclusive cybersecurity briefings, threat advisories, and a free copy of the "Top 10 Cloud Security Misconfigurations" framework.
End-to-end encryption simulated. Zero spam guaranteed.Got Scammed?
Report cyber fraud immediately. Every minute counts.